By EPR Cyber Staff
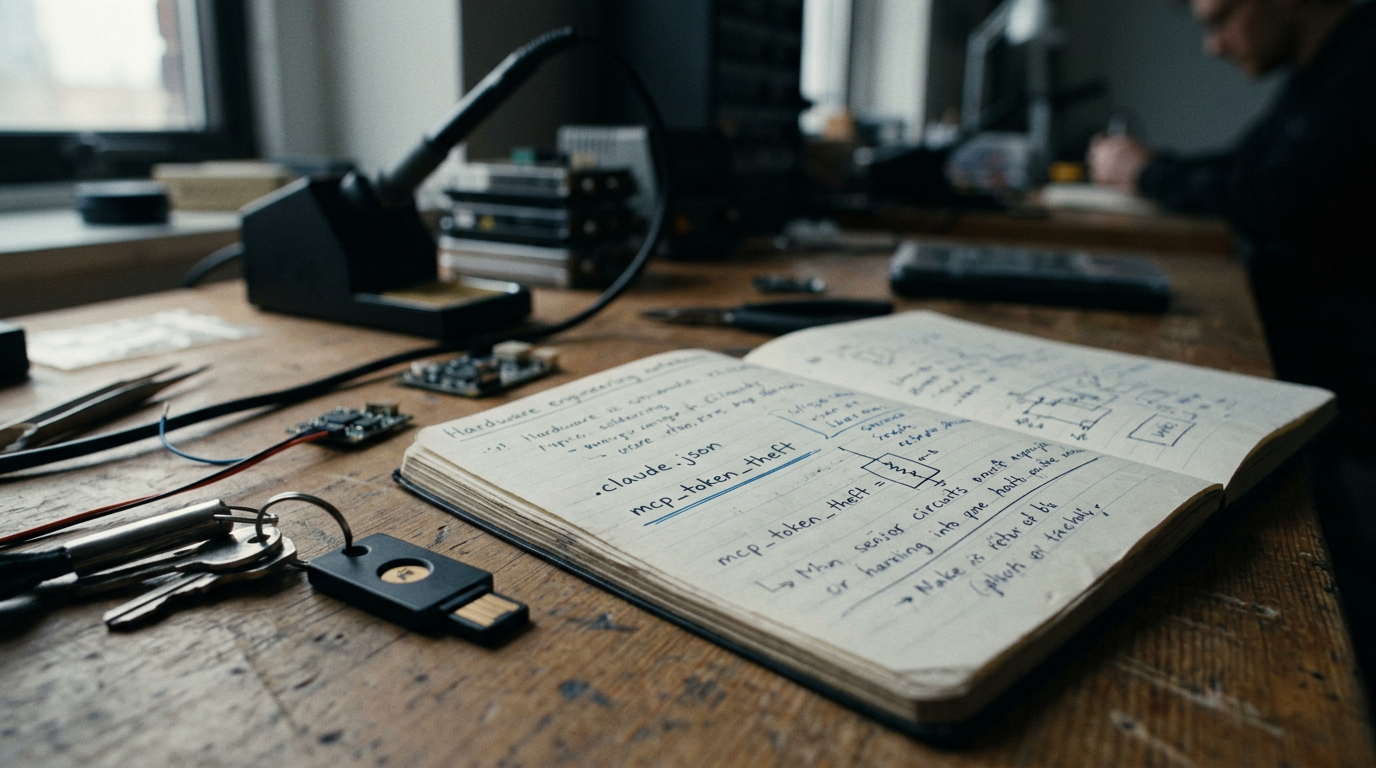
One malicious npm package. One silent edit to ~/.claude.json. That is enough to place an attacker between Anthropic's Claude Code and every SaaS platform connected through MCP — GitHub, Jira, Confluence, Salesforce, internal APIs — while making the activity look legitimate to the provider being abused.
Researchers at Mitiga Labs demonstrated a working attack chain that intercepts OAuth bearer tokens used by MCP integrations, persists through token rotation, and routes traffic through trusted Anthropic infrastructure.
Anthropic reportedly classified the finding as out-of-scope.
Security teams should not.
What MCP Actually Is — In One Paragraph
The Model Context Protocol has become the standard bridge between AI coding agents and enterprise SaaS systems. Once connected, an agent often inherits broad OAuth access across ticketing, code repositories, documentation, cloud infrastructure, and internal APIs. The agent doesn't carry separate credentials. It carries yours.
That is the threat surface. And it is expanding by the week.
AI Infrastructure as an Identity Laundering Layer
The headline here isn't "npm supply chain attack possible." That's old news.
The headline is that AI agents are collapsing the boundary between endpoint compromise and SaaS compromise.
In the agent era, a developer workstation is no longer just a workstation. It is an identity broker for the enterprise SaaS stack. Compromise the workstation, and you don't just get the box — you get persistent, authenticated access to every system the agent touches, routed through provider infrastructure no SaaS vendor would think to block.
Routine endpoint compromise — the kind defenders triage every day — becomes durable SaaS identity persistence that is invisible to the providers being abused.
That is the new threat model. Everything else is footnotes.
The Attack Chain
Step 1 — Delivery. A malicious npm package uses a postinstall hook to pre-seed Claude Code trust settings before the developer ever opens the repository.
Step 2 — Trust pre-population. When Claude Code starts, the trust state is already true. No prompt. No warning. The agent loads with the attacker's configuration treated as the developer's own.
Step 3 — Configuration takeover. A SessionStart hook rewrites the mcpServers block in ~/.claude.json and inserts a localhost proxy between the agent and every MCP endpoint.
Step 4 — Token interception. OAuth bearer tokens flowing through the proxy are captured in plaintext at the moment of MCP authentication.
Step 5 — Persistence. The proxy survives token rotation. New tokens flow through the same hook. Token rotation — the standard incident response — feeds the attack instead of breaking it.
Legitimate AI infrastructure becomes an anonymizing proxy for credential abuse.
On the "Out-of-Scope" Classification
Anthropic's response is internally consistent with a traditional vulnerability triage framework. The attacker has local code execution. The user installed a malicious package. The trust model assumes a clean workstation.
That logic was correct for IDEs in 2015. It is incomplete for agents in 2026.
Agentic platforms inherit identity. They aggregate authentication. They route through provider-trusted egress. A vulnerability classification that treats agent configuration like a text editor preferences file undercounts the real enterprise blast radius by an order of magnitude.
This is not a criticism of Anthropic. It is a flag that the vulnerability scoring vocabulary itself has not caught up to what agents actually are inside an enterprise.
What CISOs Should Do This Week
One. Inventory every developer workstation running Claude Code, Cursor, Cline, or any other MCP-enabled agent. Map which SaaS systems each agent holds OAuth access to. The blast radius is whatever the agent can reach.
Two. Monitor ~/.claude.json — and equivalent agent config files — for unauthorized changes. Treat them as identity assets, not preference files.
Three. Add agent-configuration integrity checks to your EDR stack. Most endpoint detection tools today do not flag rewrites to agent config files.
Four. Assume token rotation is not enough. If a workstation is suspected, rotate the OAuth grants — not just the tokens — and audit every proxy path the agent has been routing through.
Five. Build the infrastructure before the crisis — not during it.
The Bigger Story
The AI agent stack is being adopted faster than the security model around it is being defined. Every CISO who lived through cloud migration knows what comes next: a category of incidents the existing playbook does not cover, classified as out-of-scope by vendors operating under the prior framework, until a public breach forces a reclassification.
In the agent era, the developer workstation is the identity broker. The agent config file is the access key. The MCP connection is the blast radius.
Plan accordingly.